When the State Decides Your Model Is a Weapon
TL;DR: If frontier AI becomes decisive in war, private companies will not retain full control over how it’s used. The legal tools to compel cooperation already exist. The only uncertainty is timing. Position yourself near governance, infrastructure, and compliance chokepoints before the autonomy narrative collapses.
Silicon Valley believes it can draw moral boundaries around artificial intelligence.
Washington believes it can draw national ones.
If those lines ever collide, there will not be a philosophical debate. There will be a decision.
In early 2026, Palantir CEO Alex Karp warned the tech industry plainly: companies trying to reshape the global economy while refusing defense cooperation are deluding themselves. If a capability becomes strategically decisive, he argued, the government will not negotiate indefinitely. It will act.
That warning was not ideological. It was structural.
Once a technology materially influences military outcomes, it stops being a product. It becomes infrastructure.
And infrastructure is governable.
The Quiet Shift From Innovation to Sovereignty
Frontier AI is no longer just a productivity layer.
It analyzes intelligence at scale. It compresses logistics cycles. It models conflict scenarios. It accelerates cyber operations. That makes it dual-use by default — not by accident, not by misuse, but by nature.
Some labs have tried to draw moral “red lines” around military applications. The instinct is understandable. The impulse to protect a technology from its darkest uses is, in its own way, admirable. But geopolitics does not respect corporate mission statements.
China’s 2017 national AI strategy explicitly integrates civilian and military objectives under state direction from the outset. AI is treated as sovereign infrastructure.
If American labs insist on autonomy while adversarial states integrate seamlessly, the asymmetry grows.
Asymmetry creates pressure.
Pressure eliminates optionality.
That progression is not hypothetical. It is historical.
The Mechanism Already Exists
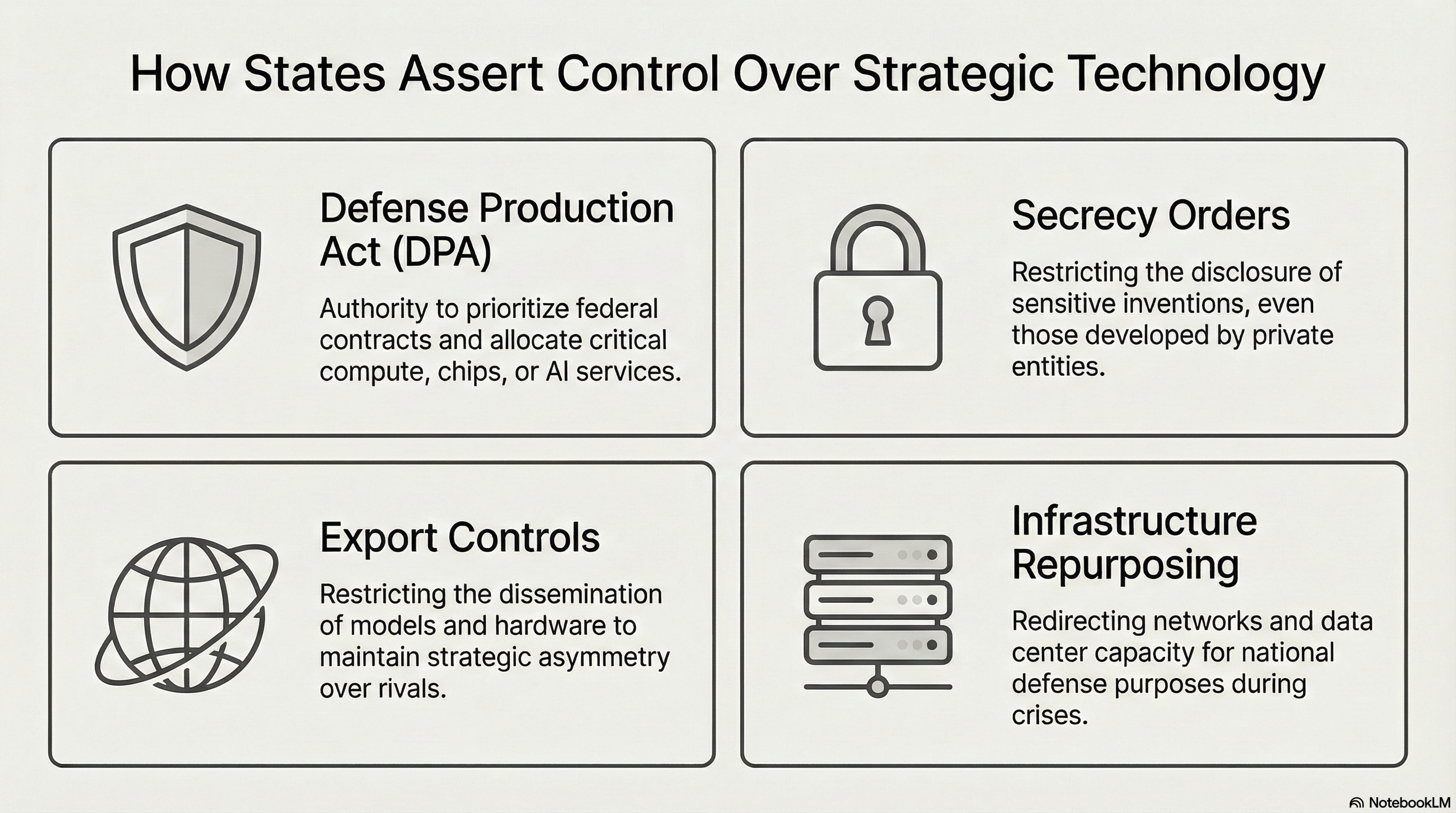
No dramatic new law is required to bring frontier AI under state direction. The legal architecture is already in place, and has been for decades.
The Defense Production Act (1950) allows the executive branch to prioritize defense contracts and direct the allocation of facilities, materials, and services.
The Invention Secrecy framework empowers the government to suppress inventions deemed sensitive to national security.
Export controls already restrict dissemination of advanced technologies across borders.
History fills in the pattern.
In 1918, President Wilson assumed control of telegraph and telephone systems under wartime authority. During World War II, resistant manufacturers were nationalized or compelled into compliance.
The mechanism was different each time.
The logic was the same.
When survival is framed as the issue, corporate autonomy narrows.
Not because founders lack intelligence.
Not because their concerns aren’t legitimate.
But because sovereignty outranks leverage.
The Illusion of Refusal
There is a persistent belief in parts of the tech world that refusal equals leverage. That if a company declines cooperation, the state will eventually compromise because innovation is too valuable to disrupt.
This misunderstands power.
States possess statutory authority, procurement leverage, and monopoly on force.
Companies possess capital and talent.
In peacetime markets, capital dominates.
In strategic crises, authority dominates.
The rules change — and they change fast.
You do not need tanks in the street to see the direction of travel.
Why This Matters Beyond Defense
The implications extend well past any particular contract or any particular lab.
If frontier AI becomes sovereign infrastructure — meaning state-directed, nationally controlled, auditable on demand — the civilian economy reorganizes around that fact.
Access tightens.
Compliance requirements expand.
Approved-model lists become standard operating procedure.
Audit trails become mandatory.
Governance stops being a maturity signal and becomes the cost of admission.
If your company depends on open, frictionless access to frontier models, you are implicitly betting that private control remains stable under geopolitical stress.
History suggests that bet weakens as pressure rises.
The question is not whether state intervention is possible.
The legal tools make that obvious.
The question is: when — and what triggers it.
Surviving the Shift
You do not survive regime changes by arguing online.
You survive by positioning near the control points before those control points become obvious to everyone else.
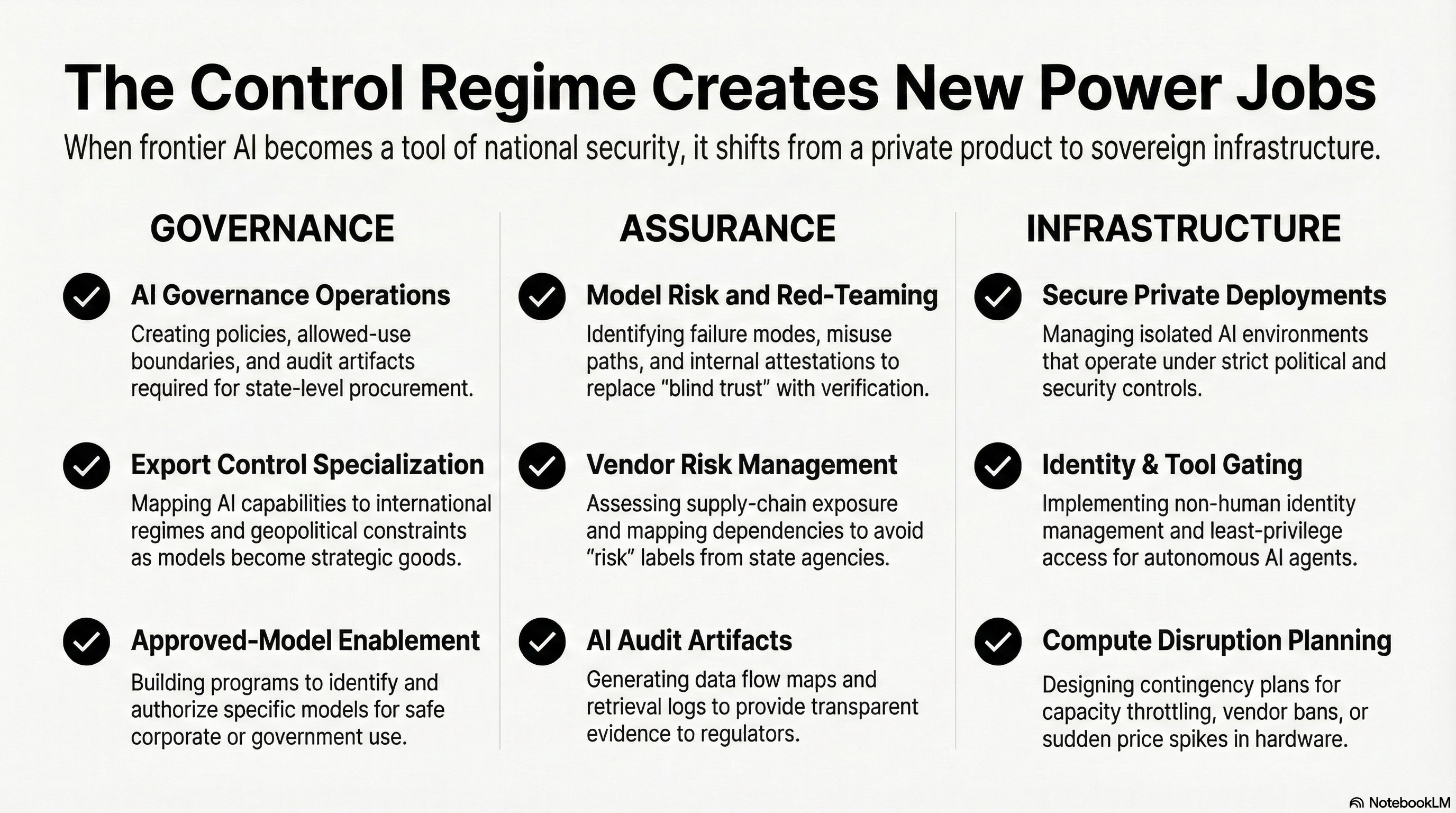
When infrastructure becomes sovereign, power concentrates in three places:
- Governance
- Assurance
- Infrastructure control
The people who understand those systems — who built careers around them before they became fashionable — will not be scrambling.
They will be essential.
The future does not belong only to better prompt engineers.
It belongs to people who understand:
- Where data flows
- Who controls compute
- Under what legal authority
- How auditability works in practice
- What export regimes apply
- How procurement language reshapes markets overnight
These are not glamorous skills.
They are durable ones.
Career Repositioning Signal
If you are early in your AI career, stop optimizing for “AI fluency.â€
Optimize for AI control fluency.
The most resilient paths over the next five years are not pure model builders — they are:
- AI governance operators
- Model risk and evaluation specialists
- AI vendor risk and procurement experts
- Secure AI infrastructure architects
- Export-control and compliance strategists
When access becomes political, companies do not pay for creativity first.
They pay for control.
Be the person who understands the control architecture.
7 / 30 / 90 — Position Before the Trigger
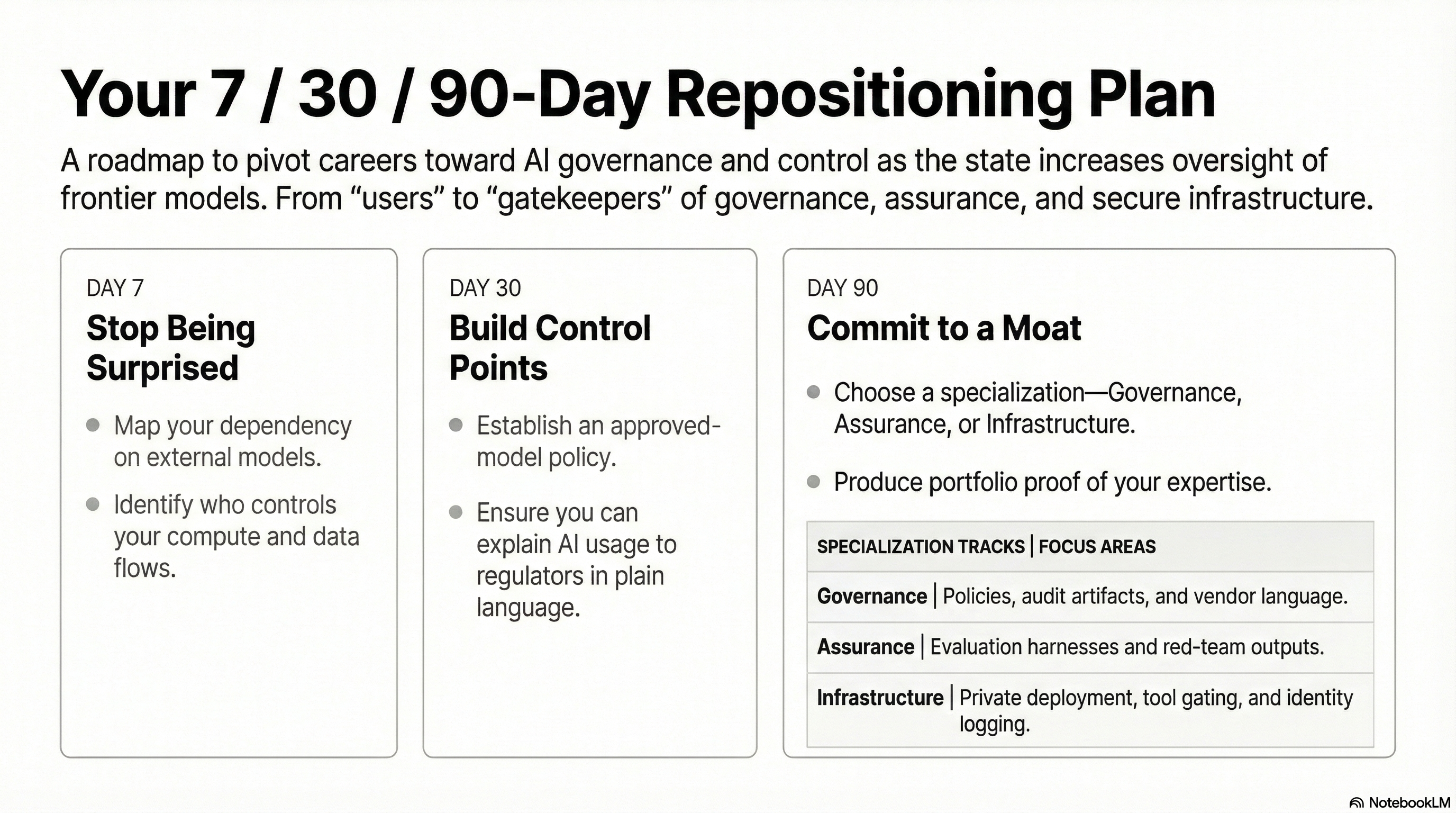
Next 7 days:
Map your dependency on external models. Identify where your data flows, which vendors control your compute, and what you would lose if access became conditional.
Next 30 days:
Implement logging. Define an approved-model baseline. If you cannot explain your AI usage to a regulator in plain language, you are exposed.
Next 90 days:
Choose a path and commit. Specialize in governance, assurance, or infrastructure. Build tangible proof of capability before demand spikes.
When pressure rises, companies scramble for people who already understand control systems.
Be that person before the scramble begins.
The Only Real Uncertainty
No one can identify the precise trigger.
It could be a geopolitical flashpoint.
A decisive cyber event.
A compute bottleneck designated a national defense resource.
A procurement standoff that escalates unexpectedly.
The specific scenario is unpredictable.
The direction is not.
The tools for state coercion already exist.
If frontier AI becomes genuinely decisive — if it shifts outcomes tied to national survival — private red lines will not hold.
The state will not ask permission.
Position accordingly.